Please go to my new blog
November 18, 2012 Leave a comment
Technology-enabled excellence in Commercial Finance and Leasing
May 30, 2012 Leave a comment
The government is planning £100m in funding for alternative lenders, including new internet finance firms.
It is part of £500m being made available to small and medium sized firms through the government’s Business Finance Partnership.
So called peer-to-peer lenders are expected to be big beneficiaries. They use the internet to match businesses with investors with money to loan
July 15, 2011 Leave a comment
With summer holidays coming up and international roaming data at £1 for 1mb – thats one email with an attachment, it’s time for drastic action.
May 9, 2011 Leave a comment
I can’t comment on what someone who can’t be said to be a banker was up to when the Crunch hit. The buzz when Twitter user @injunctionsuper spilled the beans was mainly around the celebrities named.
@Ruskin147 – Rather weird that Twitter has been alive with super-injunction details for weeks – but one new account with inaccurate reports is news
@DorothyKing – If we’re not “allowed” to know who has a #superinjunction how do we know who not to discuss? Goldsmith? Ryan Giggs? Fred Goodwin? Branson?
@TheSpacePope – Anyone think @injunctionsuper got one wrong deliberately to allow trad media to be able to report the story? #superinjunction
However less was said about the conduct of those at the helm of an industry whose collapse cost the UK taxpayer £1trillion – perhaps because they have deeper pockets. But even if you get a “Contra Mundi” super-injunction it can’t redact the internet rumours altogether.
But I can’t say anything.
Except to point out that sometimes even recent history repeats itself:
http://www.telegraph.co.uk/news/uknews/1573557/Northern-Rock-chief-had-affair-before-collapse.html
April 29, 2011 Leave a comment
More is coming out about the loss of the “keys to the Kingdom” at RSA.
For a great discussion of this and other security topics follow the Security Now! Podcast and the archive at GRC.com
In short a user just opened a spreadsheet.
A small group of RSA employees received a targeted spearfishing email, which got intercepted and moved into their spam folders.
Steve Gibson continues:
But one of the employees in one of these small groups looked in her junk mail folder, and the email was titled “2011 Recruitment Plan.” And she opened the email, and there was an attachment, 2011 Recruitment Plan.XLS, making it a Microsoft Excel spreadsheet. That she opened, and that allowed a Flash movie, an Adobe Flash file that was embedded in the spreadsheet with an at-that-time unknown exploit, a zero-day flaw which Adobe has since patched, that allowed it to run. And that installed a well-known trojan which is freely available on the Internet called “Poison Ivy.” It’s a so-called RAT, an R-A-T, a Remote Administration/Access Tool/Toolkit trojan, which then phoned home, that is, it called outwards from her machine to a remote server that gave bad guys essentially the ability to do anything that she could do from her machine, they could do. And that’s all it took. That was their foothold in RSA. And the rest, as they say, is history…
The incident highlights two major security issues.
Firstly however much you warn people not to open attachments from sources they don’t know, the hackers will always come up with something so tempting – such as the promise of video of a tennis star -that someone, somewhere will just have to open it. And it only takes one. That’s social engineering!
The second is equally challenging to solve.
Adobe have rightly earned their place on every desktop, laptop, tablet and smartphone (except for Flash on Apple IOS!) by providing software for rich media.
A PDF document will always display a document as it would appear on the printed page – but it can extend beyond that to include video and links to the page. When filing my company return earlier in the year, I downloaded a PDF from the Companies House , filled it in. The PDF document validated my return and then transmitted the return off with the click of a button. Most useful when you have four hours left before the filing deadline.
No multimedia or social networking site would survive now without Adobe Flash videos. Celebrating the Royal Wedding I am stiing with the live YouTube courtesy of Flash and even the programme with animated page turns.
However to provide this rich media the Adobe software has system powers far beyond what you would expect for a “reader” or “player” software. And the Adobe software is cross platform – common across browsers (Internet Explorer, Firefox, Chrome, Safari, Opera) and Operating Systems (All versions of Windows, Mac OS, Unix) so the products provide a big target for exploits.
My Adobe Reader has 21 Plugins – from a vanilla installation – allowing internet access, sending mail, reading out loud, updating, and the Adobe EScript plug-in ‘that allows PDF documents to take advantage of JavaScript’.
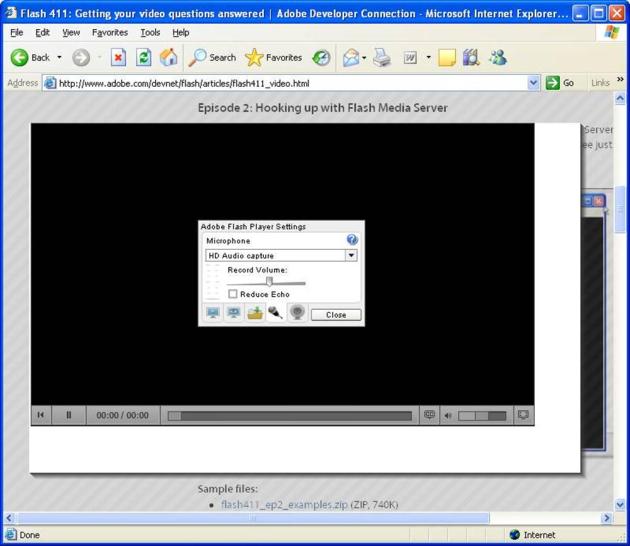
Right click on any flash plug in and look at the settings. There flash can take over your hardware including the microphone and the webcam. It can put a file anywhere the user can – including the installation of malicious software.
Adobe are belatedly patching vulnerabilities – and seem to be giving up on their lethargic quarterly update frequency. Adobe Reader X (I’m no sure if that’s an “ex” or a “ten”) is starting to introduce a sandbox to isolate Adobe from the core operating system.
So what can be done to avoid these vulnerabilities?
However it would be a brave IT manager to try to take Adobe reader and Flash away from users, and it is a complex exercise to find substitutes. Few would have enough clout to impose the “iPhone approach” and simply say No.
April 15, 2011 Leave a comment
I was chased today to complete my overdue mandatory compliance training.
So I spent a few hours completing the training and the test. The result?
“Test Passed
The exam contained 14 questions, of which you answered 13 correctly, or 93%.
These are the questions you answered incorrectly:
April 12, 2011 Leave a comment
I get an email from McKinsey. “Someone you have never heard of has lost your data.”
I was not alone. Epsilon, a marketing services company that sends 40 billion e-mails a year has been hacked. An estimated 2% of its customer date has been “exposed”. As with the recent major leak at RSA, Epsilon has not disclosed any details of the breech. The full impact of the breech is well explained in the Economist.
The emails being sent by major companies including JPMorgan Chase, Target, McKinsey and Marks & Spencer are all in the same format:
“We have been assured by Epsilon that the only information that was obtained was your first name, last name and e-mail address and that the files that were accessed did not include any other information…We want to urge you to be cautious when opening links or attachments from unknown third parties.”
Well the files stolen DID contain some other valuable information – the trusted relationship between me and the company. The phishing emails won’t appear to come from ‘unknown third parties’ – they will look as if they have come from the company which I know, and have trusted until now.
Phishing emails are always obvious from:
Combined with a spell checker, the spear phishers behind the Epsilon leak can give the crime a quantum leap.
Here are the questions to ask any company that has been using Epsilon to email you:
Below is another boiler plate for you as I’ve had to answer this a lot. Incidentally, I looked up your account under nic@nicevans.eu, and you are just a free member so we only have your email, name, company and title – not your address. Epsilon assures us that ONLY name and email were taken. Please read on for further info.
McKinsey Quarterly deeply regrets this unfortunate circumstance. We take your privacy concerns very seriously, and we felt it was important to inform our users as soon as the facts became available to us.
As you may have seen since McKinsey Quarterly’s message to its users, McKinsey Quarterly was one of many Epsilon clients whose data was compromised. Many of our users have noted that they subsequently received breach notifications from credit card companies, reward programs, online services, retailers, etc. Epsilon is one of the largest email service providers, and, unfortunately, many have been affected.
For all affected companies and end users, Epsilon has publicly stated that the breach was “limited to email addresses and/or customer names only.” Following our message to users, Epsilon has provided further assurances to McKinsey Quarterly, specifically: “All data extracted from the platform is logged and the only data extracted/downloaded to a file was email, first name and last name.” Additionally, “the attacker was only logged into the system for a short period of time based on application logs… which would not have allowed the user to manually review (rather than download) a single record at a time.”
McKinsey Quarterly does not store sensitive personal information (such as account passwords, financial information, or other personal identity details) with Epsilon. We urge our users never to respond to emails requesting sensitive information and to be cautious when opening links or attachments from unknown third parties.
Epsilon has detailed for McKinsey Quarterly security measures put into place since the breach, and they are working with appropriate legal authorities in an ongoing investigation. McKinsey Quarterly is separately undertaking its own review of Epsilon and email service providers, in general, and we can assure our readers that we will endeavor to ensure the highest security of our users’ information.
Again, McKinsey Quarterly deeply regrets the inconvenience to our valued readers. Thank you for your continued patience, understanding and readership.
Sincerely Yours,
Rik Kirkland
Senior Managing Editor,
McKinsey & Company
April 1, 2011 Leave a comment
The IT security world was rocked by the publication of an open letter, written by security vendor RSA boss Art Coviello on 18 March.
In the letter he said the company had ‘identified an extremely sophisticated cyber-attack in progress’. ‘An investigation has led us to believe that the attack is in the category of an Advanced Persistent Threat’. In layman’s terms that means that a burglar broke in, the alarms didn’t go off, and they were there for quite a time.
‘The attack resulted in certain information being extracted from RSA’s systems. Some of that information is specifically related to RSA’s SecurID two-factor authentication products.’ Just about anyone who has used a corporate Virtual Private Network in the last ten years will be familiar with these tokens which display an apparently random 6 digit number that changes every minute or so. This number is used together with some other password (two factors) to log-in.
I am sure this letter will become a case study in damage limitation – see my earlier blog “Sorry seems to be the hardest world“. This was a clear example of the minimum necessary disclosure approach. There was much speculation at the Financial Sector Technology Expo in London today about what might have been stolen. “If I knew, I couldn’t tell you” said one Chief Security Officer. “They are only speaking to a very few of their major customers at Banks, and then under tight Non Disclosure Agreements.”
In the absence of hard facts, most informed opinion suggests the breech included the data that links the key used to generate the number to the identification number engraved on the back of each token. This is supported by advice going around that you should remove this engraved number – and RSA’s fix which is to issue replacement tokens.
So the news headlines again:
March 29, 2011 Leave a comment
Madison Kay spent $1,400 on bushels of Smurfberries. Aside from illustrating the need for Stephanie Kay to keep one-click ordering away from her eight year old daughter, it also illustrates the bushels of money to be made from virtual worlds: with $99 for a barrow load of smurfberries in a game ostensibly for children, what money could be made for more adult products?
There have been many red faces on social networks with the appearance of FireSheep – a simple add in to the FireFox browser that allows anyone to hijack social networking sessions of other users on an open wireless network. The security hole was basic. While the login to Facebook is performed over a secure https connection the subsequent exchanges are then open. These can be eavesdropped and even hijacked: the security credentials are stored in cookies on the client and passed to the eavesdropper.
So was Facebook’s hasty move to implement secure connections, which had previously been too expensive to implement, out of concern for the privacy of their users data? There is a bigger and more direct motive for Facebook.
Many addicts of Facebook apps, such as Farmville and Bejewelled Blitz will have been tempted to get extra credits for a small credit card payment. Up until now each of these virtual worlds have had their own virtual currency. However Facebook are now making the Apps providers use Facebook credits. The spin is that it’s simpler for the single market and travellers in these virtual worlds. But most lucrative for Facebook who take a 30% commission on the exchange between real currency and Facebook credits.
And Apple makes a similar 30% on payments through its Apps store – and is similarly forcing apps providers to make payments for usage of apps through the Apps store. Which makes easy money for virtual products like Smurf’s Village – even with hasty patching forcing users to input a password for purchases. But is tough on real service providers like Spotify. Even Rupert Murdoch – whose iPad only Daily launched last month in the US – pays 30%.
These may be small amounts individually but enormous in total. The market capitalisation of Zynga, owner of FarmVille is over $5.5Billion – comparable to the merged British Airways and Iberia (IAG) $6,7Billion- so a 30% cut of their revenues is….a lot.